Hannover Messe 2019

Hannover Messe 2019
Register for Free Ticket and Be Our Guest at Hannover 2019!
Visit us at Stand C11 where we will be showcasing:
Rugged and Reliable Gateway & Router for IIoT
Event Details:
Date:
1-5 April 2019
Location:
Hannover · Germany
Stand:
Hall 8, Stand C11
Featured Products and Solutions
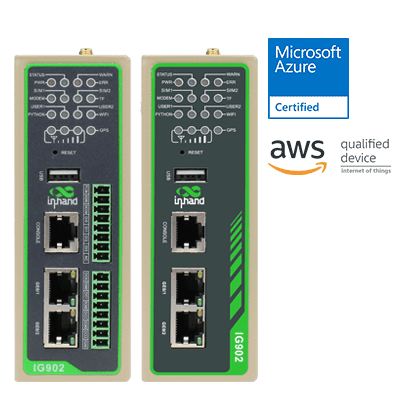 | IG902 Edge Computing Gateway + Multiple industrial protocols: Modbus TCP/RTU, OPC UA Client, EtherNET/IP, ISO on TCP, etc. |
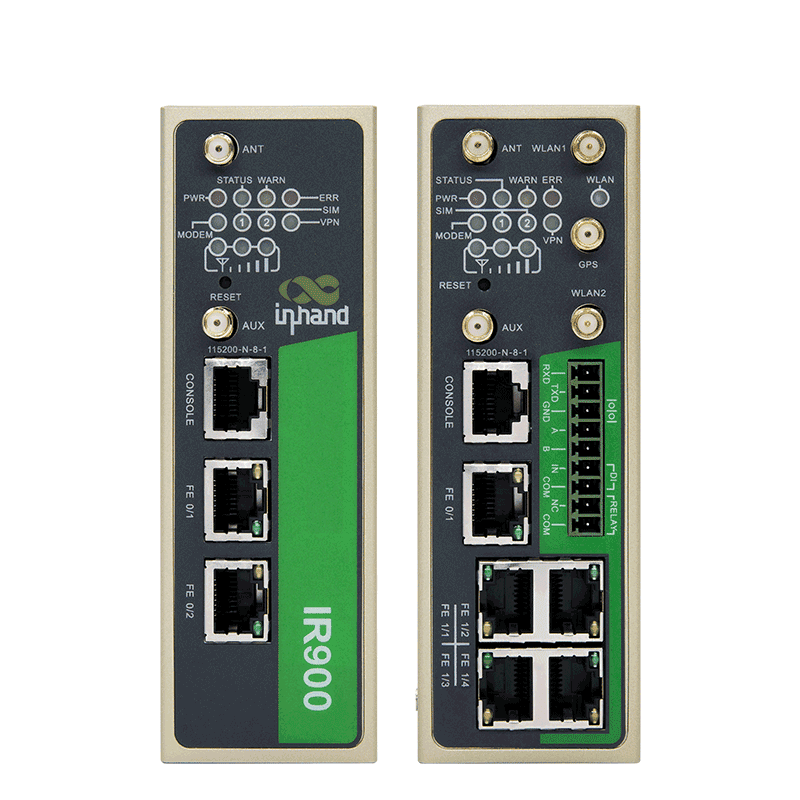 | IR900 High Performance Industrial LTE Router + Fast Deployment, High Reliability, Advanced Security |
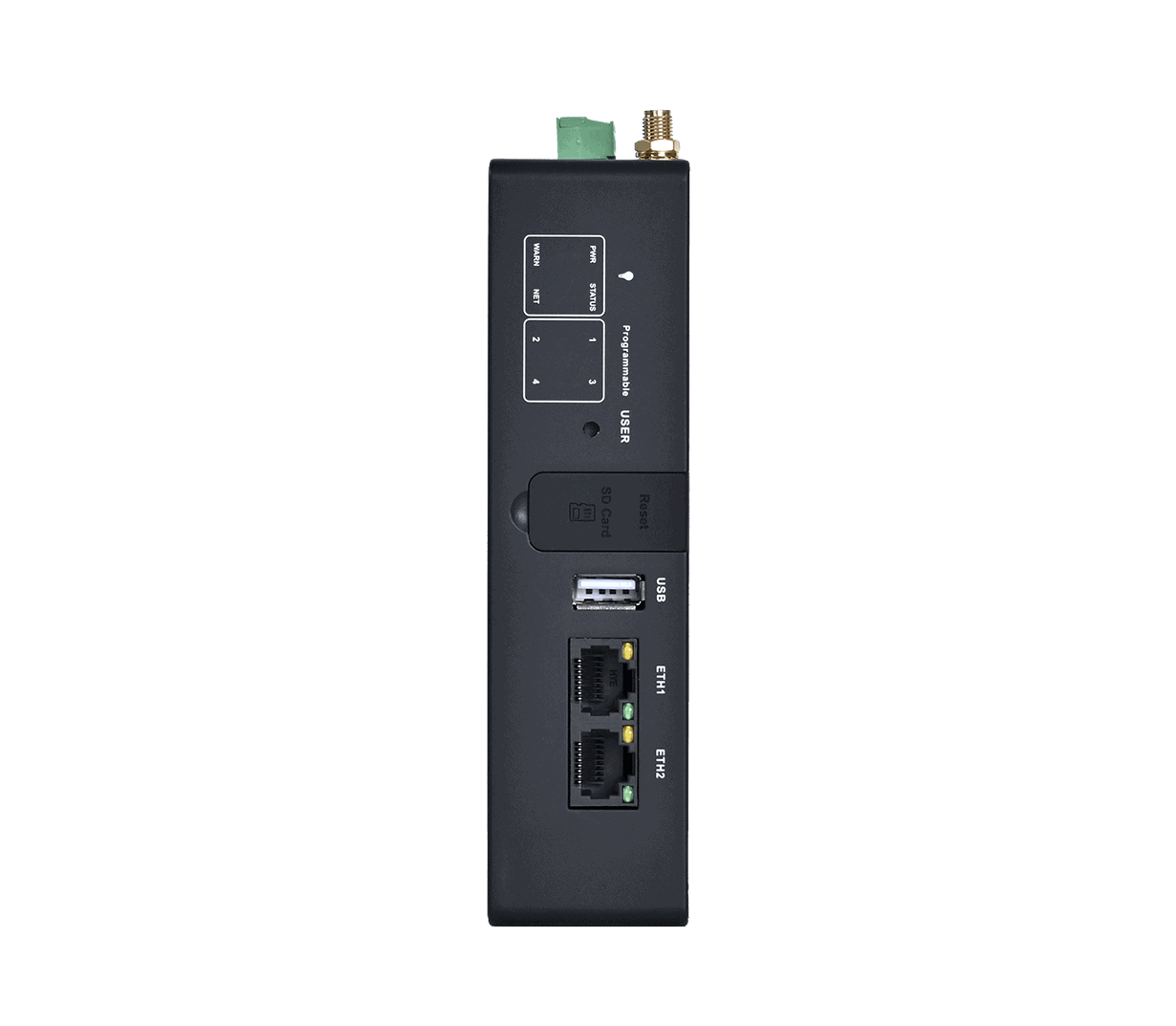
 | IR600 Industiral LTE Routers + 5*ETH ports, Dual SIM, Failover, VPN, Wi-Fi |
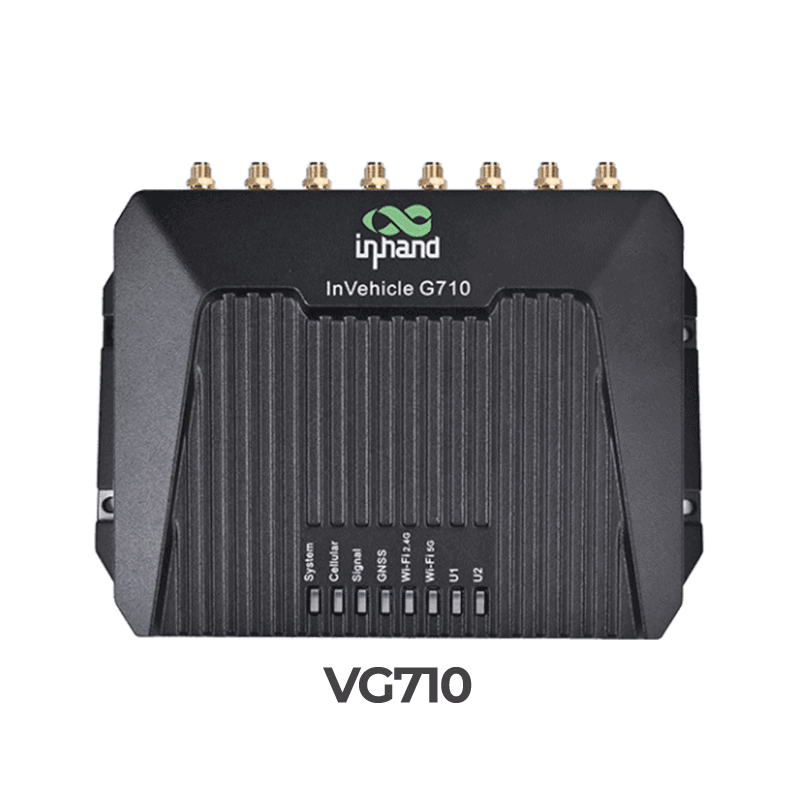 | VG710 Vehicle Gateway + LTE CAT6/4 |
Related Products
EC312
TI AM6231/1 GB RAM/8GB eMMC/4G/Wi-Fi
Edge Gateway

AI Edge Computer
1-157 TOPS Industrial AI Edge Computer
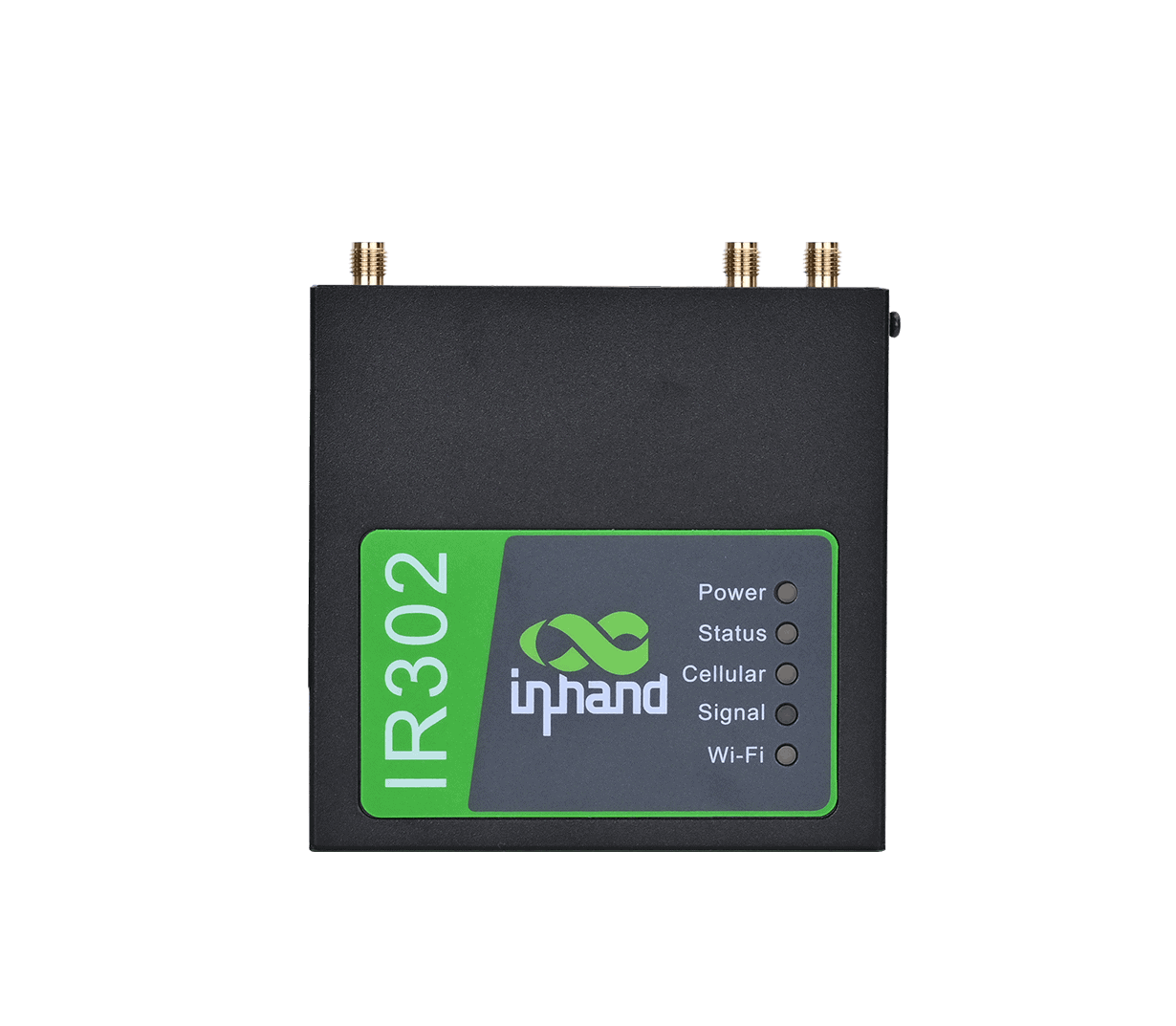
Industrial Router
Highly Reliable Industrial-Grade LTE Router

Edge Gateway
Multi-Protocol IoT Gateway Designed for IoT Applications

Vehicle Gateway
4G/5G Vehicle Gateway the Internet of Vehicles

